Experts Matter. Find Yours.
Connect for media, speaking, professional opportunities & more.

Responding to increased pressure, Facebook has "doubled down" on identifying and removing posts by online extremists and the groups they use to share content. As noted in a recent NBC News article, these increased efforts include using artificial intelligence and machine learning to proactively identify and remove posts and groups that break the rules, and promoting tools that would hold group administrators more accountable for posted content." Megan Squire is a professor of computer science who has conducted extensive research tracking connections between online hate groups and how they leverage social media platforms to recruit new members and spread propaganda. Squire told NBC News that she's skeptical that even these more high-tech efforts will meaningfully curtail the activity of online extremists. “Same stuff, different day,” Squire told NBC News. “Just in the past month, I reported groups calling for a global purge of Islam, extermination of people based on religion, and calling for violence through a race war, and Facebook’s response was that none of these groups was a violation of community standards.” If Dr. Squire can assist with your reporting about social media and online extremism, please reach out to Owen Covington, director of the Elon University News Bureau, at ocovington@elon.edu or (336) 278-7413. Dr. Squire is available for phone, email and broadcast interviews.

Meet Your Newest Job Recruiter, the Algorithm – let our experts explain
Equal employment opportunities may not be part of a computer’s calculations, but one engineer from is trying to change that. When you apply for a job, chances are your resume has been through numerous automated screening processes powered by hiring algorithms before it lands in a recruiter’s hands. These algorithms look at things like work history, job title progression and education to weed out resumes. There are pros and cons to this – employers are eager to harness the artificial intelligence (AI) and big data captured by the algorithms to speed up the hiring process. But depending on the data used, automated hiring decisions can be very biased. “Algorithms learn based on data sets, but the data is generated by humans who often exhibit implicit bias,” explains Swati Gupta, an industrial engineering researcher at Georgia Tech who’s work focuses on algorithmic fairness. “Our hope is that we can use machine learning with rigorous mathematical analysis to fix the bias in areas like hiring, lending and school admissions.” But as algorithms harness speed and efficiency – how can they be adjusted to include and consider race, gender and other human factors? It’s an area Dr. Gupta has been researching and refining. If you are a reporter or journalist looking to cover this topic – that’s where our experts can help. Dr. Swati Gupta is an Assistant Professor in the H. Milton Stewart School of Industrial and Systems Engineering at Georgia Tech. Dr. Gupta is an expert in the areas of optimization, machine learning, and bias and fairness within the AI sphere. She is available to speak with media regarding this topic - simply click on her icon to arrange an interview.

Cybersecurity expert aims to protect the power grid by hacking would-be hackers
For hackers, the U.S. energy grid is a treasure trove of classified information with vast potential for profit and mayhem. To be effective, the power grid’s protection system has to be a bit like a hacker: highly intelligent, agile and able to learn rapidly. Milos Manic, Ph.D., professor of computer science and director of VCU’s Cybersecurity Center, along with colleagues at the Idaho National Laboratory (INL), has developed a protection system that improves its own effectiveness as it watches and learns from those trying to break into the grid. The team’s Autonomic Intelligent Cyber Sensor (AICS) received an R&D 100 Award for 2018, a worldwide recognition of the year’s most promising inventions and innovations. “An underground war of many years” Manic calls foreign state actors’ ongoing attempts to infiltrate the power grid — and efforts to thwart them — “an underground war of many years.” These criminals aim to enter critical infrastructures such as energy systems to disrupt or compromise codes, screens login information and other assets for future attacks. The nightmare result would be an infrastructure shutdown in multiple locations, a so-called “Black Sky” event that would erase bank accounts, disable cell phones and devastate the economy. In that scenario, engineers would have less than 72 hours to restore the grid before batteries, food supplies, medicine and water run out. With high stakes and increasingly sophisticated attackers, artificial intelligence and machine learning are key to respond to the challenges of protecting the grid’s interconnected systems, according to Manic. “Hackers are much smarter than in the past. They don’t necessarily look at one particular component of the system,” Manic said. “Often they can fool the system by taking control of the behavior of two different components to mask their attack on a third.” A nervous system for the power grid Using artificial intelligence algorithms, AICS can look holistically at an array of interconnected systems including the electrical grid and adapt continually as attacks are attempted. It is inspired by the body’s autonomic nervous system, the largely unconscious functions that govern breathing, circulation and fight-or-flight responses. Once installed, AICS acts as a similar “nervous system” for a power grid, silently monitoring all of its components for unusual activity — and learning to spot threats that were unknown when it was first installed. To “hack” the hacker, AICS often deploys honeypots, shadow systems that appear to be legitimate parts of the grid but that actually divert, trap and quarantine malicious actors. These honeypots allow asset owners to gather information that can help identify both a threat and a potentially compromised system. “Honeypots can make a hacker think he has broken into a real system,” Manic said. “But if the hacker sees that the ‘system’ is not adequately responding, he knows it’s a honeypot.” For this reason, the system’s honeypots are also intelligently updating themselves. Manic developed AICS with his INL colleagues Todd Vollmer, Ph.D., and Craig Rieger, Ph.D. Vollmer was Manic’s Ph.D. student at the University of Idaho. The AICS team formed eight years ago, and Manic continued to work on the project when he came to VCU in 2014. He holds a joint appointment with INL.

China Employs Mass Surveillance as Authoritarian Tool in Xinjiang Province
China has been engaged in high-tech surveillance of citizens in its Xinjiang province, according to a New York Times report, creating “an incubator for increasingly intrusive policing systems” that could expand automated authoritarianism across the country and abroad. One of the prime motivators, ostensibly, is to monitor and subdue minority religious and ethnic groups. This practice presents obvious, multi-faceted ethical issues, says Benjamin R. Mitchell, PhD, an assistant professor in Villanova’s Department of Computing Sciences with expertise in computer ethics. “The Chinese government surveillance project in Xinjiang is a perfect example of why we must be cautious and thoughtful about the deployment of technology. Most of the basic technologies being deployed were not originally developed for this application, and many of them have alternative uses which are potentially beneficial, or at the very least less clearly harmful to human rights. But applying these technologies to the surveillance and oppression of large groups of citizens still requires a large, intentional effort, making this as much a social and moral problem as it is a technological one.” Modern technologies, constantly being refined and developed, have brought us closer to the potential spread of totalitarian states, Dr. Mitchell says. “George Orwell’s 1984 was intended as a cautionary tale, but there have always been authoritarian regimes that have viewed it as a how-to manual. In the past, however, the manpower requirements for implementing such a system made it impractical to scale up to very large target groups. Modern technologies like automatic facial recognition and machine learning are now beginning to make widespread deployment of such systems possible.” Decreasing costs of technological surveillance systems will make their misuse even more likely, and those that employ them are justly open to criticism and opposition, Dr. Mitchell noted. “While the cost and manpower requirements are still likely too high to deploy such a system nationwide, the costs are steadily being driven down through research and development, meaning the development of a totalitarian information state is easier than ever before. It is entirely appropriate to critique governments, companies, or individuals who knowingly contribute to the construction and deployment of systems intended to oppress.” Although technology plays a key role in the Chinese attempt to oppress or eliminate targeted groups within its own borders, it is certainly not the first of its kind to do so through authoritarian surveillance, says Dr. Mitchell. “We can look at examples like Nazi Germany or Soviet East Berlin to see how this type of surveillance and suppression has been used in the past; the technological sophistication may have been less, but the risks to human dignity and freedom were broadly the same. The technology is certainly an enabling factor, but the fundamental problems presented here are not new ones. Security is important for human flourishing, but we must remember that the targets of pervasive surveillance can never feel secure; in pursuing security thoughtlessly, we can destroy it. If we are to be moral, we must consider the security of all people, not just those in a position of power,” he concluded.

MEDIA RELEASE: CAA rolling out new predictive technology
New predictive technology, created in-house at CAA South Central Ontario (CAA SCO) can now predict the likelihood of a roadside event occurring in a specific geographic area, and send a truck to that area before a breakdown occurs. CAA's new Gen 2 predictive technology gets the right truck, to the right place, at the right time. Gen 2 is a proprietary machine-learning algorithm that leverages data from 115 years of roadside assistance service. It layers on weather and humidity indicators, along with real-time traffic and GPS information to predict roadside needs. Gen 2 was developed in-house by CAA in late 2017 and piloted in the London area in January 2018. Initial results during the pilot period showed a promising reduction in the average time of arrival for roadside service vehicles. CAA SCO was able to rescue members an average of 11 minutes faster during the summer of 2018, when compared to the summer months of 2017. The service improvement is directly tied to the roll out of CAA's new predictive technology. The system learns over time, so CAA SCO expects average wait times will continue to improve. The technology has already garnered interest from roadside assistance clubs from around the world. CAA Gen 2 is currently being operationalized across CAA SCO's territory. Source:

Consumer word-of-mouth and social media
Certainly, marketers are well aware of the value of the consumers’ word-of-mouth (WOM) endorsements of a product or service. But the ubiquitous nature of social media demands that advertisers find new ways to tap into how consumers interact and communicate to leverage the power of WOM online. Panagiotis Adamopoulos, assistant professor of information systems & operations management; Vilma Todri, assistant professor of information systems & operations management; and Anindya Ghose (NYU-Stern) take a close look at the role of hidden personality traits of online users and how they play into the effectiveness of product WOM on Twitter. The trio used big data, machine learning methods, and causal inference econometric techniques to study consumer purchases made through Twitter accounts. The research showed an increase in the likelihood of a purchase by 47.58% when there was exposure to WOM tweets from a sender who had similar personality traits to the recipient of the information. The trio found that introvert users were much more accepting of WOM versus extrovert users. They also noted agreeable, conscientious, and open social media users are more effective influencers. The combinations of personality traits of disseminators and recipients of WOM impacted the decision to buy a product, with the researchers noting that a “WOM message from an extrovert user to an introvert peer increases the likelihood of a subsequent purchase by 71.28%.” Source:
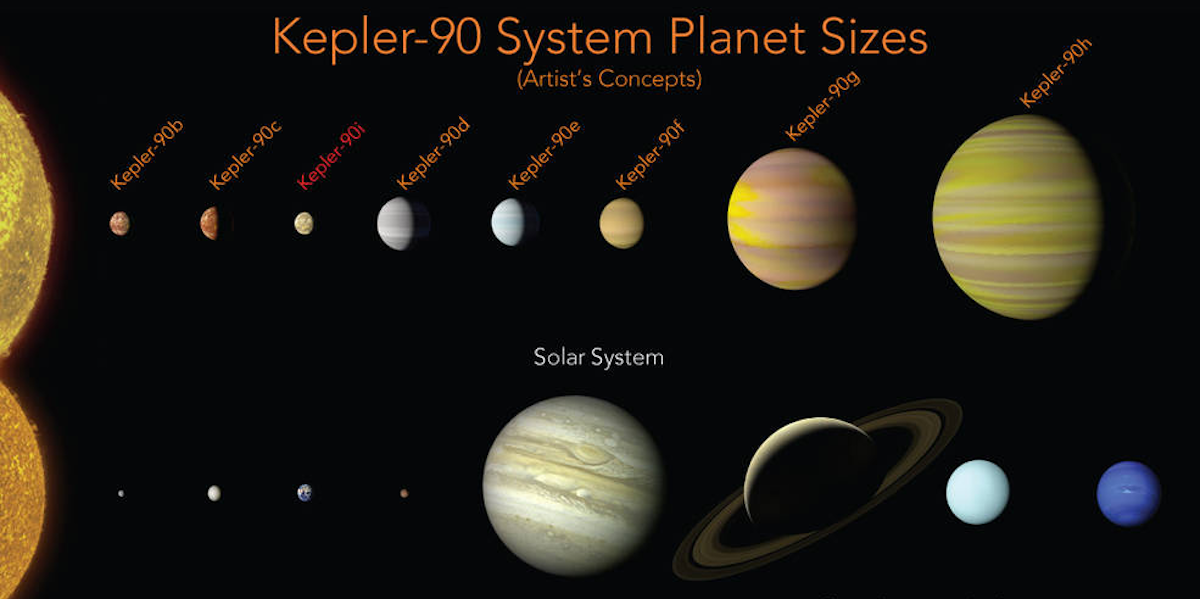
Another planet discovered by NASA – 2,545 light-years from Earth
Today, the scientific world was watching as NASA made a big announcement. Its Kepler Space Telescope, which has been conducting an intensive planet-hunting mission since 2009, had new results to share with the public. A media release from NASA states: “Our solar system now is tied for most number of planets around a single star, with the recent discovery of an eighth planet circling Kepler-90, a Sun-like star 2,545 light years from Earth. The planet was discovered in data from NASA’s Kepler Space Telescope. The newly-discovered Kepler-90i – a sizzling hot, rocky planet that orbits its star once every 14.4 days – was found using machine learning from Google. Machine learning is an approach to artificial intelligence in which computers “learn.” In this case, computers learned to identify planets by finding in Kepler data instances where the telescope recorded signals from planets beyond our solar system, known as exoplanets." There are some very technical and scientific data and information here. As well, a lot of questions to be asked and answered. That’s where experts like Dr. Michael Reed from Missouri State University can help. Dr. Reed is a professor of astronomy at Missouri State. He researches extrasolar planets and pulsating stars. Dr. Reed is available to speak to the media and can explain what this all means for science, the study of space and if there might actually be life out there. Click on his icon to connect with him. Source:







